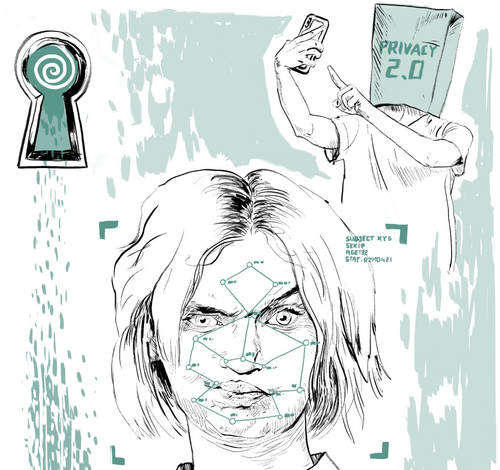
In times, where a lot of communication takes places electronically, we have to rethink our care for privacy. Currently most communication data might be stored and analized through those who are not the addressee. For maintaining privacy we need to use specific tools that make surveillance less possible or even impossible.
Beyond this defensive motivation there could be another reason for showing interest for technical tools for protection. Privacy means not only to defend ourselves against nosey pencil pushers. Through a privacy-aware attitude civil actors contributes to more quality of communication and shape spaces of confidentiality.
Privacy Risks
- Information collection: Surveillance, interrogation
- Information processing: Aggregation, identification, insecurity, secondary and third use, exclusion
- Information dissemination: breach of confidentiality, disclosure, exposure, blackmail, appropriation, distortion, increased accessibility
- Invasion: intrusion, decisional interference
Source: Solove, D. J. (2006). A Taxonomy of Privacy
Into the Internet of Everything
The growing ubiquitous computing is challenging our private sphere. Technically the intimate space cannot anymore be separated from its environment, our most discreet emails are not laying in a drawer under the towels but very often on servers out of "our four walls" somewhere. Our discrete things, a pregnancy app or a fitness tracker, are tracking sensitive body data and saving them maybe as long as a drawer would keep them. In contrast to the analogue world, creating a private intimate environment relies heavily on the cooperation and sense of responsibility of others. Even if we treat our apps and services as friends, it is not necessarily true that we want them always to be very close to us. Privacy includes also the right to remoteness, invisibility or disconnection.
In the Internet of Everything, the opportunities for use and abuse increase as data processing and collaboration between devices behind their owners’ backs intensify. When the private sphere is the space closed to the public and the space for intimacy, smart devices and smart homes can also be seen as an invasive technology potentially enabling IT companies and states to execute control in our private spheres. Sometimes an overall social goal such as navigating a pandemic outbreak by collecting and analysing personal data might be accepted, but often not.
Also interesting:
Self-protection
Privacy as a right is the legal response to the danger of potential interception. E-Privacy is the response of Human Rights to the challenges of digital transformation in regard to our privacy. New security and surveillance gaps arise in the Internet of Things, if we talk about a smartwatch, a lightning bulb or a printer.
Edward Snowden on Privacy:
"What really matters is to be conscious of the principles of compromise. How can the adversary, in general, gain access to information that is sensitive to you? What kinds of things do you need to protect? Because of course you don’t need to hide everything from the adversary. You don’t need to live a paranoid life, off the grid, in hiding, in the woods in Montana.
What we do need to protect are the facts of our activities, our beliefs, and our lives that could be used against us in manners that are contrary to our interests. So when we think about this for whistleblowers, for example, if you witnessed some kind of wrongdoing and you need to reveal this information, and you believe there are people that want to interfere with that, you need to think about how to compartmentalize that" (The Intercept, 2015).
Approaches to privacy protection are in line with Snowden’s recommendation. For instance, the use of integer apps for messaging or browsing. Password messengers protect against phishing. Websites can be accessed through anonymising browsers (like TOR) inhibiting effectively data extraction or the share of system information (location, browser, operating system).
In consequence, devices that we have not paid much attention to for a long time are gaining in importance. The domestic router is the increasingly security-sensitive device and regular software updates are becoming more and more important. Another problem is the lack of security and encryption built in to concrete devices. For instance, WiFi passwords are, in some smart devices, stored in clear text allowing others to extract them and later to access a home network with this information. Other devices have standard passwords (like bulbs, locks, or thermostats). In this regard, a budget bulb could allow the intrusion of a home network.
Introductions into Privacy and Tracking
Learn about your data shadow and to protect privacy.
Your Data Mirror
Learn about the mechanisms of data collection and the impact this practice on society. By Interactive Media Foundation.
onlineLearn, what your browser is saying about you
Dennis Anons Analyzer is demonstrating it.
onlineSurveillance Self-Defense
Tips, tools and how-tos for safer online ommunications by the Electronic Frontier Foundation
onlineICTs, data and vulnerable people: a guide for citizens
published by the Panelfit project
DownloadCover your tracks
Explore, how trackers view your browser (by the Electronic Frontier Foundation)
onlineTerms of Service Didn't read
Check the quality of popular platforms' ToS (Terms of Service)
onlineOnline Privacy Checker
A guide provided by Kaspersky
OnlineFacial recognition technologies: a primer
by Algorithmic Justice League, MacArthur Foundation
DownloadDIGIT Manifesto and guidelines for adult educators
Boost Competences for responsible online identity
DownloadSecurity in a Box
Front Line Defenders and Tactical Tech Collective gives an overview over general aspects and tools for privacy protection.
OnlineData Detox Kit
Tactical Tech Collective's instructions with focus on datafication and data-abuse.
onlineMotherboard Guide to Not Getting Hacked
A comprehensive guide to digital security
OnlineTravel Guide to the Digital World
For Human Rights defenders by Global Partners Digital. DownloadMe and my shadow
Tactical Tech Collective's introduction into tracking technologies
OnlineHolistic Security
A Strategy Manual for Human Rights Defenders including an additional trainers' manual.
DownloadStealingurfeelin.gs
Augmented movie, introduction into tracking by Noah Levenson
OnlineHow normal am I?
Interactive introduction into datafication by Tijmen Schep and Sherpa project
OnlineAre you you?
Interactive documentary and challenge: Beat face recognition systems by Tijmen Schep and Sherpa project
Online
The Digital Self
from the DIGIT-AL project Digital Transformation in Adult Learning for Active Citizenship
DownloadHuman Rights Guide
Learn about data & provacy as human rights in the guides created by Baltic Human Rights Society in EN, LV, RU
Online
General Data Protection Regulation (GDPR)
The European regulation is enforcing citizens' rights and therefore regulating the tasks of data collecting businesses and organizations (entities). It is not affecting private persons.
- A short introduction in the regulation and the tasks provided by European Commission
- For more background: Watch the documentary about the development of the regulation:
Biometric Mass Surveillance
Biometry is according to the GDPR technology using "personal data resulting from specific processing relating to the physical, physiological or behavioural characteristics of a natural person, which allow or confirm unique identification of that natural person" (Article 4 (14). On the one hand, this technology is used for individual identification (for example, to unlock a smartphone). However, when it is used to recognize and track people in social space, or to aggregate personal data about these people from the different areas of their daily lives, it becomes a social risk.
Video: What is biometric mass surveillance and what can you do about it?
Source EDRi - European Digital Rights
See also:
Passwords
Some words about passwords: Principles & Criteria, Password Manager, Saving Passwords in Browsers, Checks
Principles & Criteria
- The longer your passwords the better.
- At least: One capital letter, one number, 6 letters
- No dictionary words and publicly available information about yourself
- Consider using a phrase
- Different passwords for different services
- Update them regularly
Password Manager
The best electronic tool does not help, when your password is written in an email that is saved in an online email account. Here it can easily be read out. Therefore passwords should better be stored in a more safe place in digital wallets. If you use them, you need only to know one password for accessing the database of such a software. And you might copy and paste them into a form without anibody seeing the password when looking over your shoulder.
- KeePass (Linux, Win)
- IcloudKeyChain (MacOS)
Saving Passwords in Browsers (not)
- If you safe passwords in browsers, use a master password (activate it in the settings).
- Do not allow websites to "save my password" or "keep me logged in"
- If you are using FireSync or another online sync tool for storing passwords,be aware that such services could be a security gap.
Check
Is your email part of one of the big leaks? Is your password unique or as well compromitted? These two tools help you to check:
Virtual Keyboards
You know them from mobile devices as screen keyboards. But they might also prevent keyloggers from tracking your keystrokes. Virtual Keyboards are on board in Linux, Win, MacOS
File and Disk Encryption
Encrypt single files or complete disks.
Disk or USB Stick Encryption
...makes it complicated or impossible to read hard disks without authorization.
- Encryption may be activated in Android in the system settings.
- Standard software is included in Linux which allows you to activate encription during the installatlion process of your system.
- In some Windows versions you might chose Bitlocker as an encryption tool.
- In MacOS the standard program is FileVault.
- Open source solution: VeraCript
- With VeraCrypt you can also encrypt content on USB sticks or encrypt whole USB sticks. Access the congent with a computer with installed VeraCrypt. (For Windows users: copy also "VeraCrypt portable" to your USB stick - it can be started from any Windows machine while not being installed).
Lock & Screensaver
In case, that you would need to leave your computer unattended.
When you use your computer in cafés and you are on the toilet, make sure that your device is saved from nosey neighbors. A screen saver password locks your computer when the screen saver is on. Or,
- when going to the toilet, use the lock command.
Internet Traffic Encryption
WiFi, VPN
Between your computer and the internet is a connection. In cafés, Hotels, or in some public spaces you get it for free through Ethernet (internet cable) or WiFi. Please consider, that this is not confidential. The guy on the reception may even track your browser history if he uses the right programs and you don't care about traffic encryption or browsing encryption.
Access to WiFi
Especially the access to WiFi should be encrypted in order to prevent uninvited guests in your home network or on your computer. Prefer to use WPA/WPA2 networks, which ask you for a password.
VPN
A technology that helps you to surf and email save in critical environments and countries with a strong surveillance policy. This technology builds an encrypted connection to a server in a trustful environment. Therefore you access the internet through this trustful server, not directly through your hotel WiFi. VPN clients are included in Linux and MacOS. A VPN server needs to be set up, often you need to buy a license from one provider.
- User guide: How to Encrypt your Internet Traffic by Pixelprivacy.com
Your Data Center at Home: Router
Internet router, home WiFi, configuration
Update and passwords
Comparitech found out: "one in 16 home wi-fi routers tested are vulnerable to default password attacks". Also other researchers assume that even between 30% and 40% of users never updated firmware or initiated security updates of digital devices.
- And you? When did you update your router last?
How to do it
- You might control your router through a website (the user interface). For example, you might see how many devices are online and how much data volume you used and when. Here you might as well initiate updates and change passwords or set new accounts.
- Change the router access password, replacing the standard password (which is too often simply admin.
- Turn on encryption by activating (often under the menu item wireless security) the optionWPA/WPA2. Add a confidential password.
- If possible: set up a guest access (with limited rights) if you want to share your WiFi with others.
Smart Devices, Internet of Things
IoT, Smartwatches, Fitnesstrackers and other devices collecting personal data
Stocktaking
On average, each household has ten connected devices, but the tendency to adopt these tools is rising because of the availability of more available and affordable smart home technology. The more common they are, the more invisible and intuitive technology and processes become, with an ambivalent effect on people’s knowledge and awareness of them. Stocktaking can be a starting point for their control.
- How many devices do you connect via your router or mobile?
- How many meters are digitized in your household?
Update and passwords
- Update them regularily.
- Visit their configuration websites or access the preferences menu. Change standard passwords and enable security features if available.
A Question of Choice
- The devices can only work if they have Internet access. Therefore they store the access data to your private home network.
- Some are doing it in a less safe way, for instance, they are not encrypting passwords.
- In the worst case, a smart light bulb thrown away could cause a huge damage.
How Smart Must Be?
Because smartness means that your home is constantly monitored by servers outside your household and that a lot of personal data about you is stored on foreign servers, think carefully whether it is worth to you. But if you say "yes"
- ...if possible, prefer devices that store the data locally at home or on the device.
- ...turn off features that are designed to share your data (crash reports, data necessary for "improving",...
Browsing
SSL, TOR, Search, Surf History and Cookies, Tracking, Sync
SSL
SSL holds back those who would like to read the content of the websites you visited by encrypting the content during the transport from server to client. In example, when you fill out an online form. Or for finding out, which news you received in your Inbox or which password you are using in order to access your emails.
- You are using SSL transport encryption always when the URL of a page begins with https://. Always try to choose https if it is available.
- In Firefox, Chrome and Opera you might activate the plugin HTTPS-everywhere. Then you automatically access through SSL, if a website offers this technology.
TOR
TOR-Project provides browsers that hide your access data. For the servers, that you are addressing and the men in the middle between you and the website you are seen as someone else with a different IP address than your existing address. This technology works as well, when you have no VPN-connection but need to surf confidential.
- TOR Project offers tools for all systems.
Search
- Use a more private search engine like: DuckDuckGo
Clear Surf History and Cookies
Cookies are files left on your computer that track you. Unfortunately we need these for some things like webmailers or access to other webpages with a log in. But you might influence which kind of cookies might be accepted and when it will be deleted.
- You might use the option "empty cache/delete cookies" by hand.
- Try, if you may do what you want to do while blocking cookies in general. If not, then at least activate in your browser preferences: "Keep local data only until you quit your browser"
Block Tracking
- Explain your browser that in general it should not track your behavior by activating the "Do Not Track" function. Some websites care for that.
- A smart Firefox or Chrome plugin like Ghostery gives control over how your data is collected and used on sites and in ads. As well the Firefox Add-on Lightbeam
Sync
- If you are using FireSync or another online sync tool for storing passwords, bookmarks or content,be aware that such a service could be a security gap.
Trustworthy Apps on Your Mobile Device
Apps
Your mobile phone provider and network providers track you through account data, bill data, your personal SIM-number (IMSI), the number of your device (IMEI) and, if governments come into the game, as well more things (i.e. they block the access to your number during demonstrations).
Additionally app programmers try to offer you apps for free, that have the only one reason - to spy. Or why does your pocket lamp app require access to your contacts? Depending from your surrounding and activity, you should take these probabilities into account.
- Really confidential talks require to turn off your mobile phone and leave it outside of the meeting space.
- Save your device with a password.
- Encrypt your device with the onboard solutions.
- Check, how safe and privacy-sensitive your installed apps are.
- Free and Open Source is often less privacy-invasive. But not always.
Communication
Clouds, Messengers, Text Collaboration
Clouds
- Check, if your connection to the cloud is encrypted. This is the case if the URL to the cloud space starts with https://
- Check, if the providers are encrypting the cloud space, i. e. if they could have a look on your data or not.
- Take care, that they don't share meta-data and connect it with other services the providers are offering.
- The open source alternative to the big corp clouds are decentral services, which might be installed on your server or on the server of a webhoster you are trusting. Nextcloud is one of the most acknowledged open source alternatives.
- Cryptpad has high encryption standards and might be used anonymously
Messengers
- Signal: Snowden approved. Works only with mobile devices with SIM slots (smartphones). Includes self-destructing messages.
- Telegram: Safe, if you use "private chats". Works with smart phones as well as with tablets. Includes self-destructing messages.
- Threema: Not free, but safe. Servers in Switzerland.
- Jitsi: For traditionalists.
Text Collaboration
- Etherpad: A safe alternative to working together through googledoc can often be a simple and accessible tool like an Etherpad. But only when you generate a random link and only those, that should know the link know it. Open an Etherpad
- CryptPad, a privacy-by-design solution.
General, Providers, Encryption
General
- By default, email is the less safe messaging system (just as problematic like SMS). Today, messengers like Signal or Threema are encrypting content during the whole transport from author to addressee. In this sense, they could be the better choice for confidential texts.
- Transport encryption means the encrypted transport between you and the email server and between email server and addressee. This is the case when the link in your browser starts with https:// In an email client like Thunderbird, you need to activate SSL/TLS in the account settings.
- End-to-end encryption: Only the end users might read the text and not the intermediaries. If you want to encrypt your emails in this very safe way, you would need to install specific encryption modules in your email program. See more: Email Encryption
- Set up an email for each of your social network accounts: One for facebook, one for vk. If their database will be hacked, the hackers may not access all of your emails. Don't use there your real email.
- Using gmail might be a risk, as it connects diverse accounts, reads through your content and might cooperate with your government.
Providers
We are not offering a completed list or promoting certain providers. However, these two could be worth considering due to their very strong privacy features:
- POSTEO has servers in Germany and costs 1€/month
- PROTONMAIL is located in Switzerland and offers a basic free package.
KeePass
Dominik Reichl's password safe.
KeePassVeraCrypt
Open and free source file and disk encryption tool provided by IDRIX
VeraCriptTor Browser
Anonymised browsing with the TOR browser.
TOR projectPlugin: HTTPS Everywhere
uses SSL if possible for browsing with Firefox, Chrome, and Opera (provided by Electronic Frontier Foundation)
HTTPS-everywherePlugin: Privacy Badger
Stops advertisers and trackers from secretly tracking you in Firefox (provided by Electronic Frontier Foundation)
Privacy BadgerCryptPad
Privacy-by-design alternative to popular office tools and cloud services. CryptPad onlineOpen PGP Encryption
Providers and software including the email encryption standard
Open PGP
Illustrations: Felix Kumpfe/Atelier Hurra!
Nils-Eyk Zimmermann
Editor of Competendo. He writes and works on the topics: active citizenship, civil society, digital transformation, non-formal and lifelong learning, capacity building. Coordinator of European projects, in example DIGIT-AL Digital Transformation in Adult Learning for Active Citizenship, DARE network.
Blogs here: Blog: Civil Resilience.
Email: nils.zimmermann@dare-network.eu